Microsoft GRAPH API is the latest standard to automate Azure and Office 365 Ressources. Take a note that the known PowerShell Modules will be outdated any time, and Microsoft GRAPH API will be the only thing to use – My Thoughts!
Part 1 – Authentication and Azure App – Use Microsoft Graph API with PowerShell – Part 1 » TechGuy
Part 2 – Oauth2.0 – Use Microsoft Graph API with PowerShell – Part 2 » TechGuy
Part 3 – First Powershell Script to get a Teams Lis and Walkthrough – Use Microsoft Graph API with PowerShell – Part 3 » TechGuy
Part 4 – many examples – Use Microsoft Graph API with PowerShell – Part 4 » TechGuy
So, I tried to change some of my Scripts, which are using the actual PowerShell Modules to work with Graph API, and I found 1-2 Things (or even more) that could be interesting for someone out there when starting with Graph API.
So this is a Series of Blog Posts to understand Graph API and use it with PowerShell.
Authentication
The First and maybe the most important one is, the Authentication.
And to be honest, im not that Pro in Security and Authentication, but i will try to explain what I have learned.
Azure App Registration
What is always mandatory is to create an Azure App Registration, which is yery good explained here: Register your app with the Azure AD v2.0 endpoint – Microsoft Graph | Microsoft Docs
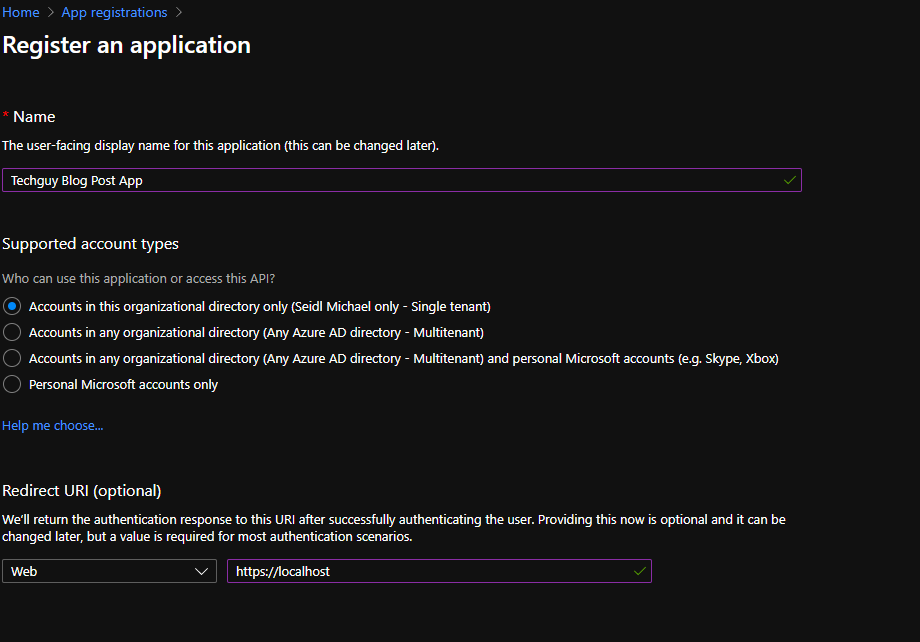
Some Note for this Link, there is no need that the redirect URL exists or is reachable, so you can enter “https://localhost”
But make sure you enter some values; in some Authentication Flows, we need a redirect URL configured.
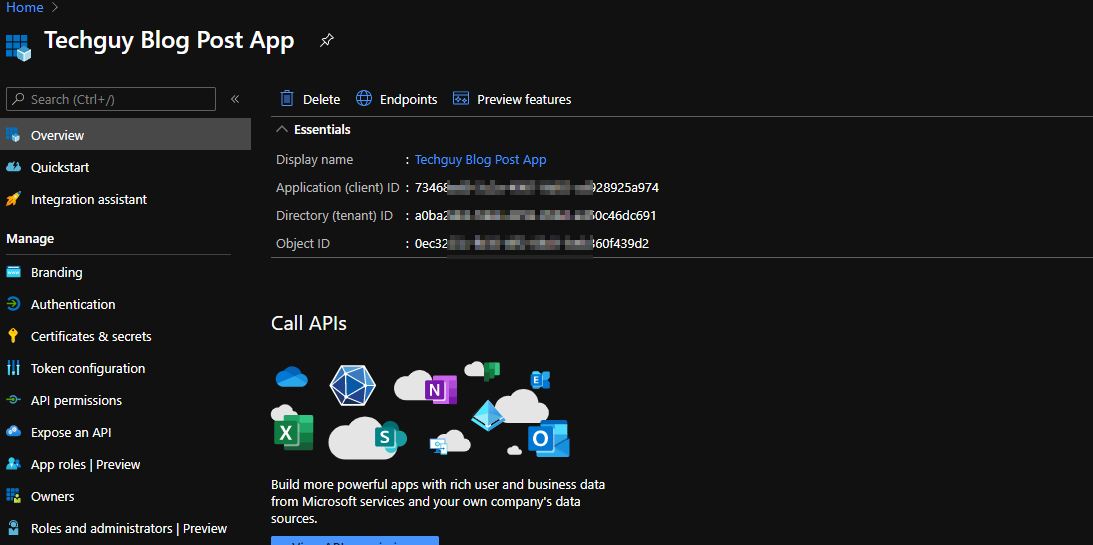
At the end you should see the Result, those ID’s are important in the later Part of this Series.
Azure APP Permissions
As we have created an Azure App now, this App needs some Permissions.
for better understanding, in your OnPrem Enviroenmnt, you have created an Service USer, and crnated them Rights to delete Exchange Mailboxes or to delete User in AD.
This App now needs also some Permissions, depending on what you try to archive
Also, a note, do not make one “Super APP” with all rights. You haven’t granted your OnPrem Service Accounts, Domain Admin Permissions, right? 🙂
Please create an App with minimal Permission for that Use-Case and create an additional App for another Use-Case.
Only the Part of Azure App API Permission can fill a huge List of Blogpost, we focus on our Scenario to automate some Microsoft Teams Task with this App
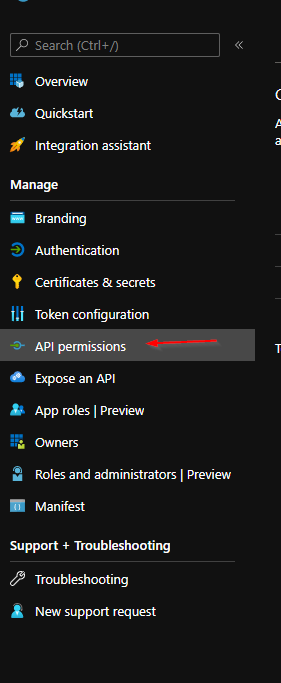
Configure API Permission
So now navigate to “API Permissions”
and select “Microsoft GRAPH”
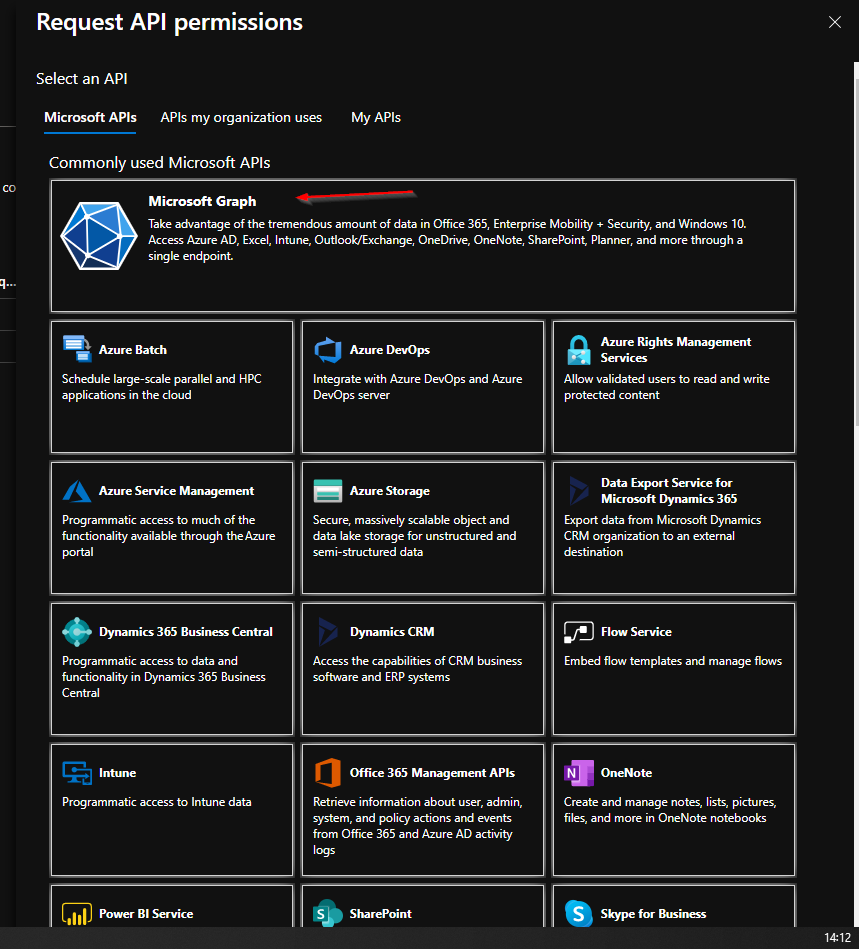
No you need to choose between “Delegated Permission” or “Application Permission”. To make the right choice let me explain a little bit further.
An “Application Permission” will grant specific Rights to a complete Application like “Teams Admin” or “Azure AD Admins.” So everyone who is using this App will get all Permissions configured with “Application Permissions”. For the user of this API, no user credentials are needed
The “Delegated Permissions” is granted to the User, which uses this App, the Permission on his Ressources. For example, you add the “Delegated Permission” to create Outlook Contacts, and the User can create Contacts in his Mailbox or Mailboxes he has already Full Access. The User is not allowed to create contacts in other Mailboxes. For this, you need “Application Permissions.” To take effect of the Delegated Permission, the User needs to provide a username and Password to use the API.
So, with the above Information, please decide which Permissions are the best for your Scenario.
In our Scenario, we would like to create, remove and update Microsoft Teams, Channels and Members, so we need the configure Application Rights.
Here is a Screenshot, of what we configured for our “Demo APP”. Microsoft did a create Job on the Documentation for Microsoft GRAP API, so on each command on the DOCS Pages, we see the needed Permissions. This will be handled in Part 2 of the Series.
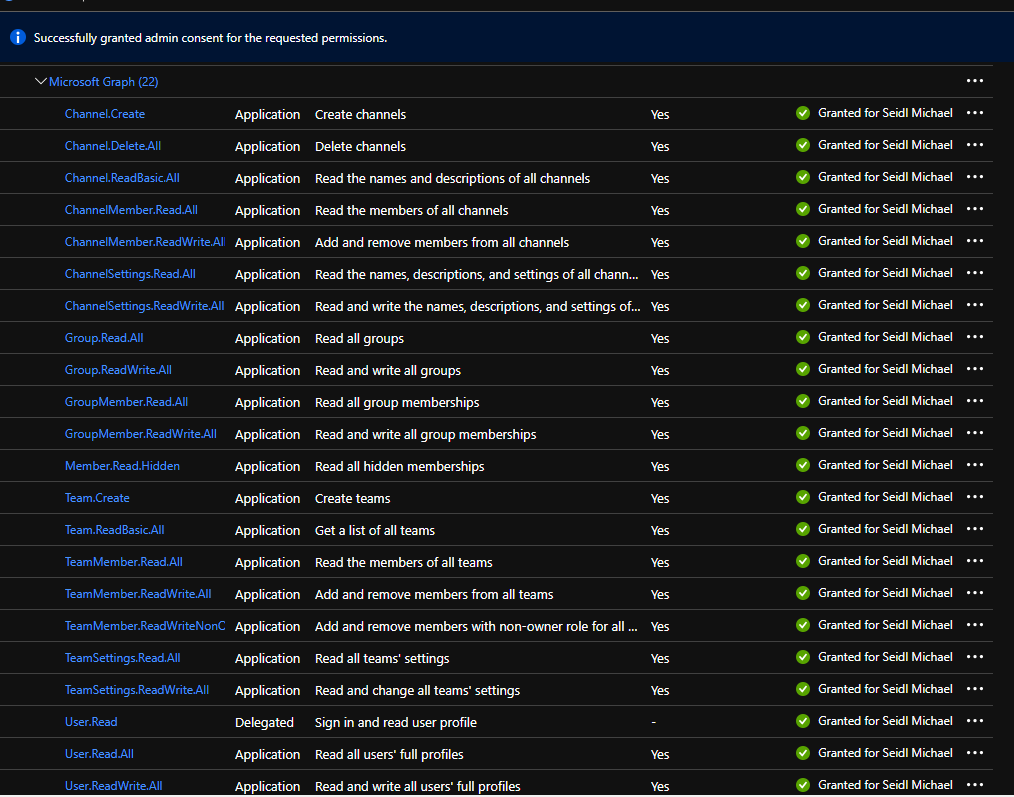
And please do not forget to click on “Grant admin consent for ***” read the Details here: Grant tenant-wide admin consent to an application – Azure AD | Microsoft Docs
Azure App Certificates and Secrets
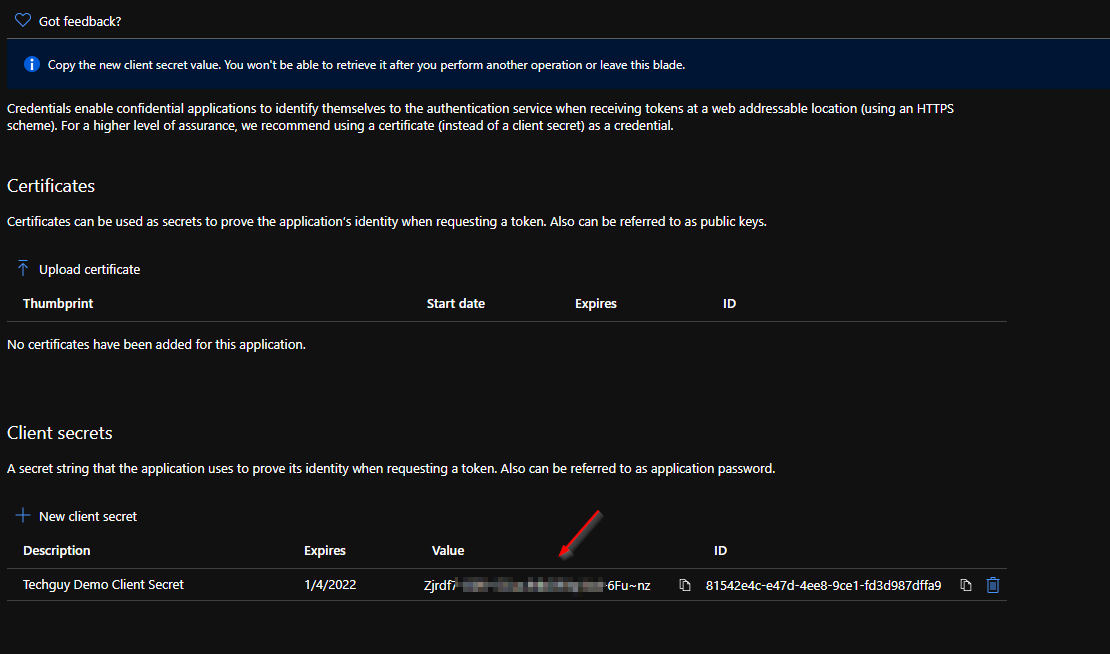
To finalize our Azure App, we need to configure the Authentication Method to use a Certificate or a Client Secret. The handling at the End is very similar, and of course, Microsoft is recommending to use a Certificate. In our Scenario, we will use the Client Secret Method.
So navigate to “Certificates & secrets”
And select “New client secret”
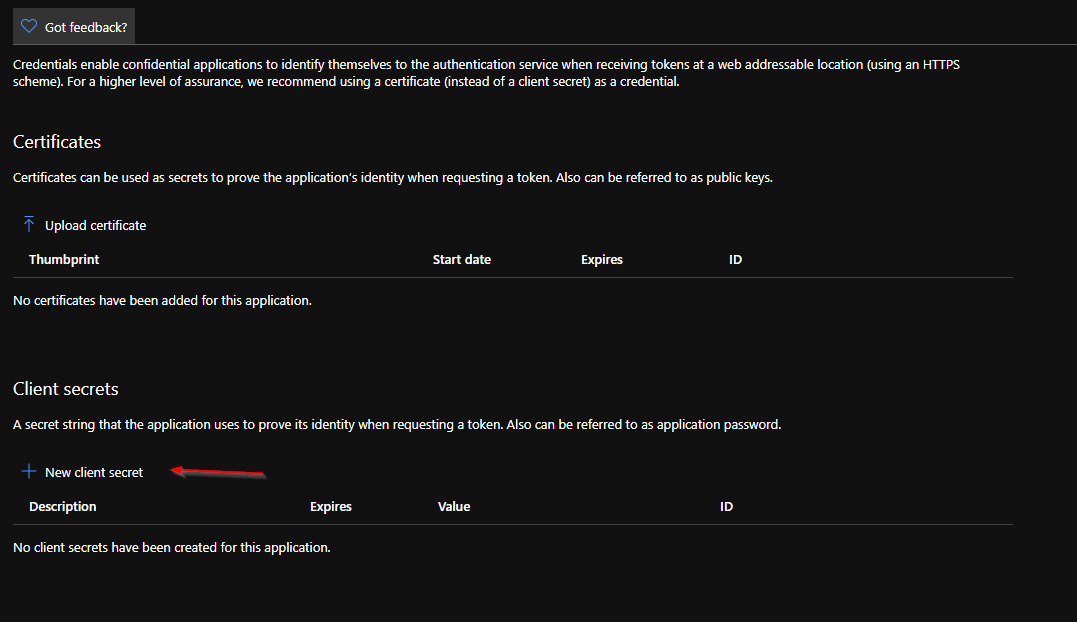
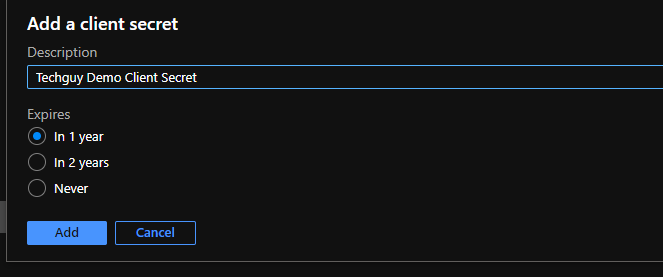
Enter a Name and Expire Date. Please choose Expire Date wisely.
!IMPORTANT!
When you click ADD, the Secret is created and you have a unique chance to get the Client Secret. This is a one-time shot, so copy the Secret, before refreshing the Page or navigating to a different Section.
So now you have prepared the Azure App, which we can use in our next Post.
Michael Seidl



Pingback: Use Microsoft Graph API with PowerShell – Part 3 » TechGuy
Pingback: Use Microsoft Graph API with PowerShell – Part 4 » TechGuy
Pingback: Paging in Microsoft Graph REST API » TechGuy
Pingback: Upload Profile Photo with MS Graph API to Azure AD » TechGuy
Pingback: Use Microsoft Graph API with PowerShell – Part 2 » TechGuy
Pingback: Send Mail with PowerShell and Microsoft Graph API » TechGuy
Pingback: Create Microsoft Team with PowerShell and MS Graph API » TechGuy
Pingback: Send Chat Message to a Teams Channel with PowerShell and MS GRAPH API » TechGuy
Pingback: Send CARD Message to a Teams Channel with PowerShell and MS GRAPH API » TechGuy
Pingback: Assign Windows 365 License with PowerShell and MS GRAPH API » TechGuy
Pingback: Set Out of Office Reply with PowerShell and MS GRAPH API » TechGuy
Pingback: Create an Azure VM with Azure REST API with PowerShell - TechGuy
Pingback: Create Microsoft ToDo Task with PowerShell and Microsoft GRAPH API - TechGuy
Pingback: Send Mail with Attachment, PowerShell, and Microsoft Graph API - TechGuy
Pingback: Enable Lost Mode for Intune Device with PowerShell and Microsoft Graph API - TechGuy
Pingback: Add a Member to a Microsoft Teams Team with PowerShell and MS Graph API - TechGuy
Pingback: Remove a Member from a Microsoft Teams Team with PowerShell and MS Graph API - TechGuy
Pingback: Create a Channel in Teams with PowerShell and MS Graph API - TechGuy
Pingback: Change a Teams Owner to a Member with PowerShell and MS Graph API - TechGuy
Pingback: Change a Teams Member to an Owner with PowerShell and MS Graph API - TechGuy
Pingback: Monitor your Azure Secrets, Zerts and SPN's Expire Date with PowerShell - TechGuy
Pingback: PSCONF EU: Use PowerShell to read Inbox and draw a contest Winner - TechGuy
Pingback: Get all your Azure Enterprise Apps with Owner and Usage Count - TechGuy
Pingback: Add an Owner to an Azure Application Registration with PowerShell and MS GRAPH API - TechGuy
Pingback: Create an Azure App Registration with PowerShell and MS GRAPH API - TechGuy
Pingback: Add a Secret to an Azure Application Registration with PowerShell and MS GRAPH API - TechGuy
Pingback: Delete a Secret from an Azure Application Registration with PowerShell and MS GRAPH API - TechGuy
Pingback: Control Azure VM with PowerShell and Azure REST API - TechGuy
Pingback: Create and delete Azure App Regs - Manage Azure App Reg with PowerShell and MSGRAPH API - Part 1 - TechGuy
Pingback: Draft Mail with PowerShell and Microsoft Graph API - TechGuy
Pingback: Monitor your Azure Secrets, Zerts and SPN's Expire Date with PowerShell - now with an Exclude List - TechGuy